
Risk Mitigation: Definitions and Steps to Guard Your Company Data from Cyberattacks
Risk mitigation is the process of identifying, assessing, and reducing potential risks that could impact a company’s data security. Using…

Risk mitigation is the process of identifying, assessing, and reducing potential risks that could impact a company’s data security. Using…

Security clearance is a status granted to individuals that allows them access to classified information or restricted areas. It is…

Root Cause Analysis (RCA) is a methodical approach to identifying the underlying causes of problems in order to eliminate them…
Penetration testing is a simulated cyberattack on a computer system, network, or web application designed to identify security flaws that…

Social engineering is a type of manipulation in which people are tricked into disclosing sensitive information or taking actions that…
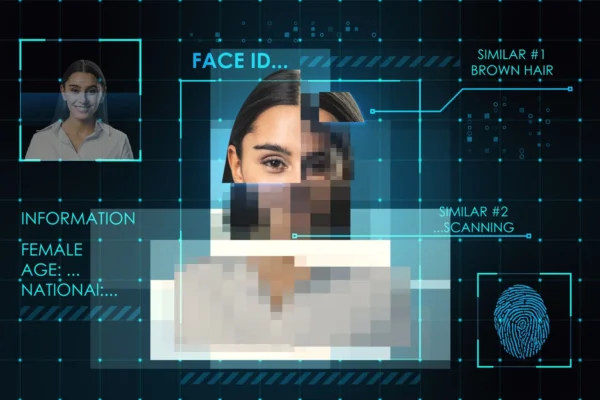
Digital identity is the online representation of an individual’s personal information and activities. It includes usernames, passwords, social media profiles,…

In cybersecurity, risk management involves locating, evaluating, and reducing possible risks that might compromise the integrity of an organisation’s digital…
Back end frameworks are tools that help developers in the process of creating and maintaining the server-side of a website…

Back-end development is the process of creating the foundation and functionality of web applications. This includes database management, server-side scripting,…

Backend security is the defense against potential cyberthreats and unauthorized access to a system’s server-side components, such as databases, applications,…